Trojan horse removal: Protecting Troy
 What is Trojan Horse Virus? | Protect
What is Trojan Horse Virus? | Protect  What is Trojan Virus | How to Remove
What is Trojan Virus | How to Remove  What is a Trojan Horse Virus
What is a Trojan Horse Virus  What is the Trojan Horse Virus
What is the Trojan Horse Virus  Trojan Viruses and How Do These Threats
Trojan Viruses and How Do These Threats  What is a Trojan Horse malware - how to
What is a Trojan Horse malware - how to  All About Trojan Horse Viruses | Just
All About Trojan Horse Viruses | Just  How To Remove Trojan Virus From Windows 10
How To Remove Trojan Virus From Windows 10  Trojan Horse Trojan War Computer Virus
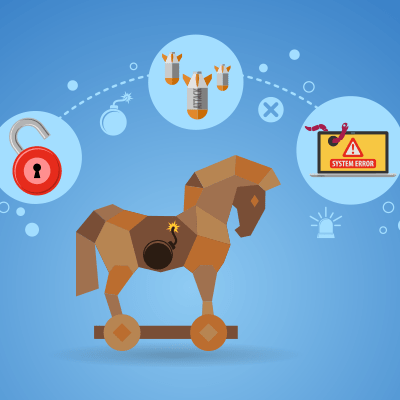
Trojan Horse Trojan War Computer Virus  What Is a Trojan Horse Attack? Plus 3
What Is a Trojan Horse Attack? Plus 3  360 Total Security
360 Total Security  PC and Devices Against a Trojan Horse Virus
PC and Devices Against a Trojan Horse Virus  3 Ways to Get Rid of Trojan Horses
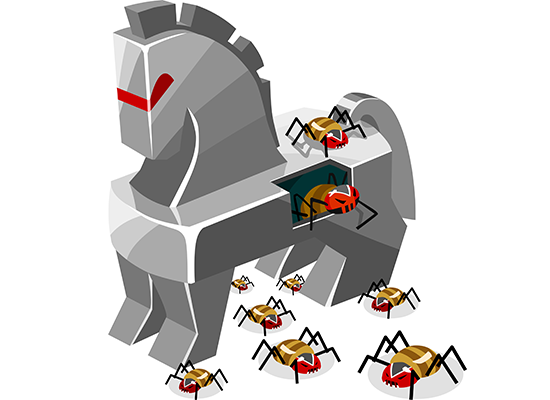
3 Ways to Get Rid of Trojan Horses  Behind the Disguise of Trojans
Behind the Disguise of Trojans  Trojan Horse Computer Virus
Trojan Horse Computer Virus  Avoiding a Trojan Virus: Keeping the
Avoiding a Trojan Virus: Keeping the  Virus, a Trojan, a Worm, and a Rootkit
Virus, a Trojan, a Worm, and a Rootkit  Computer Virus Clip Art Transparent PNG
Computer Virus Clip Art Transparent PNG  Trojan Horse, Computer Virus
Trojan Horse, Computer Virus  SPYWARE AND TROJAN HORSE INFECTIONS
SPYWARE AND TROJAN HORSE INFECTIONS  What is Malware? - Definition from
What is Malware? - Definition from  Virus, Worm and Trojan Horse
Virus, Worm and Trojan Horse  Trojan Virus Scam (Mac) - virus removal
Trojan Virus Scam (Mac) - virus removal  3 Ways to Get Rid of Trojan Horses
3 Ways to Get Rid of Trojan Horses  Computer Virus Spyware Trojan Horse
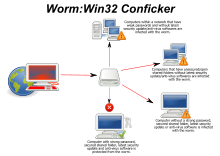
Computer Virus Spyware Trojan Horse 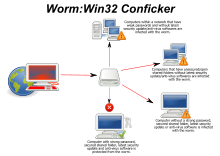 Computer worm - Wikipedia
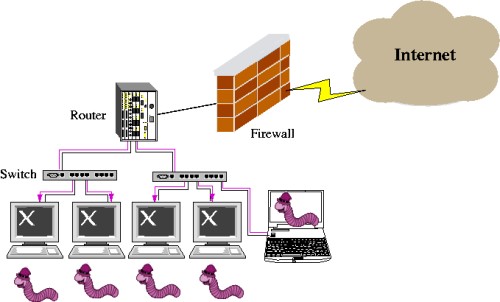
Computer worm - Wikipedia  viruses, trojans and malicious software
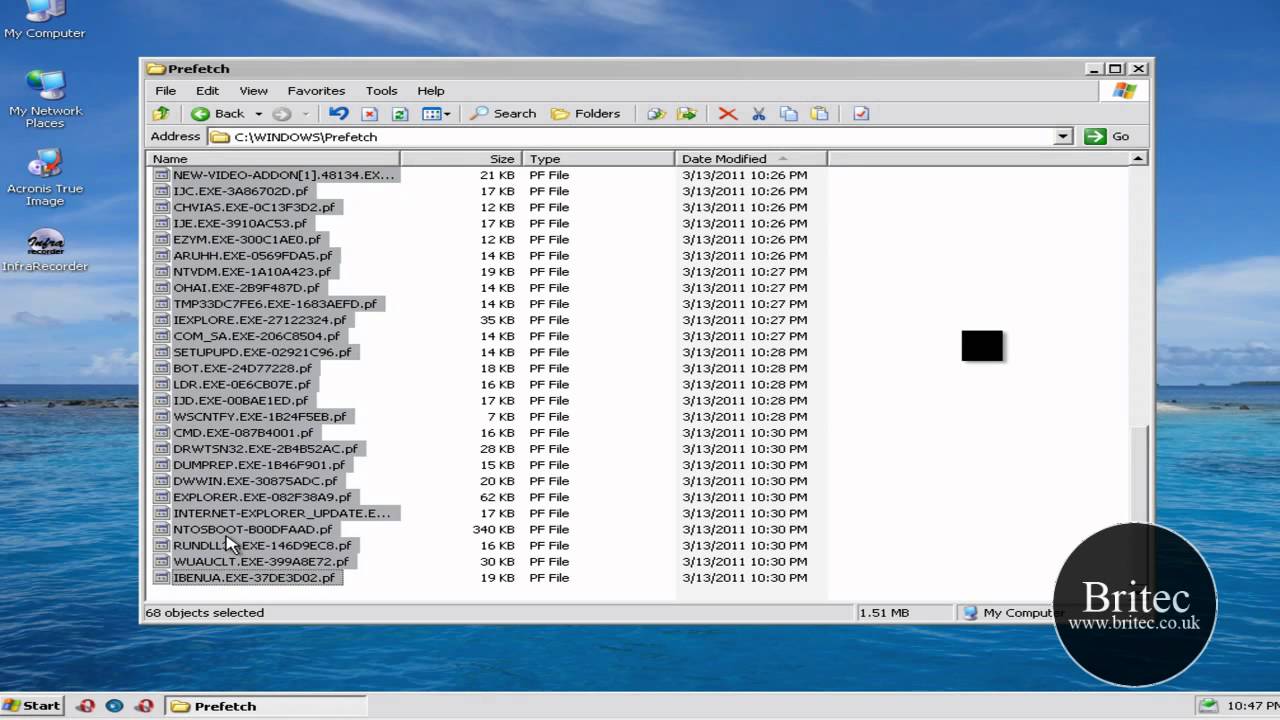
viruses, trojans and malicious software 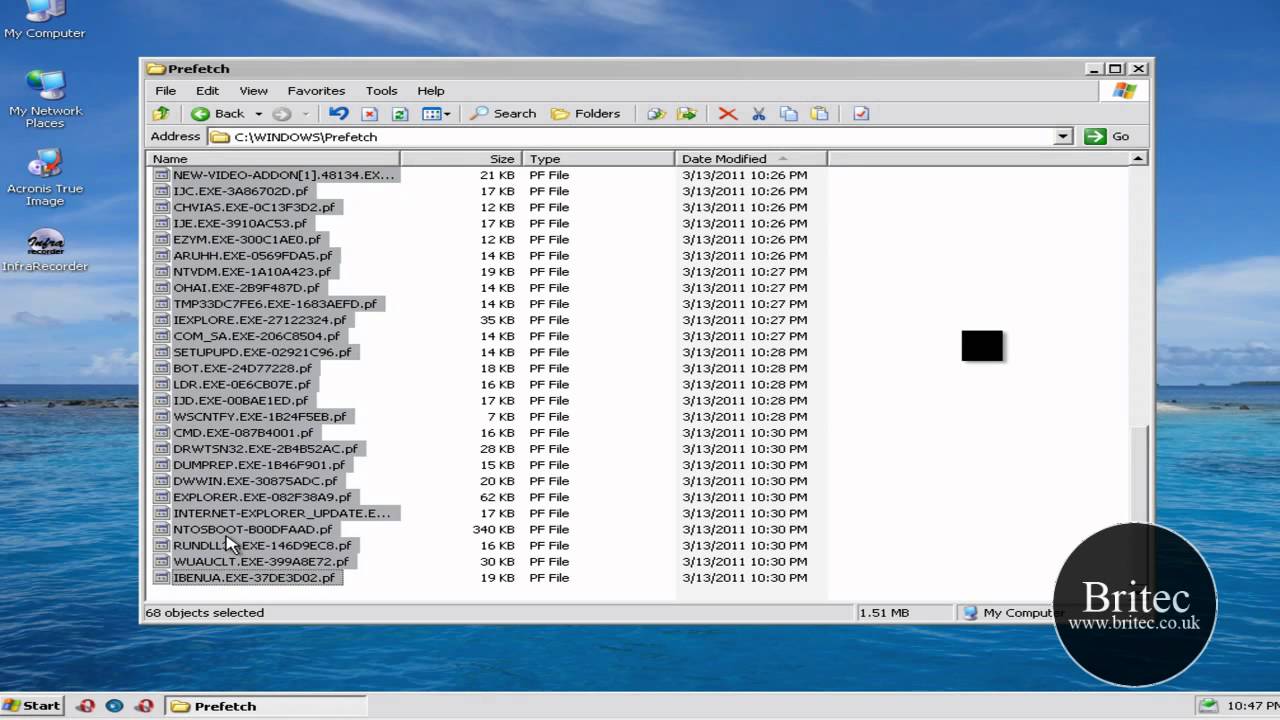 How to remove a Trojan, Virus, Worm, or
How to remove a Trojan, Virus, Worm, or 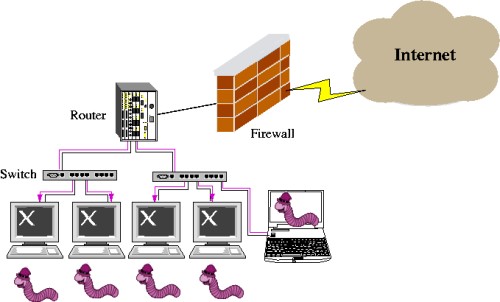 CCNA Security: Worm, Virus and Trojan
CCNA Security: Worm, Virus and Trojan 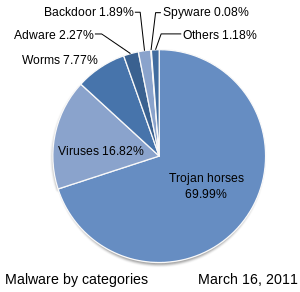 Malware - Wikipedia
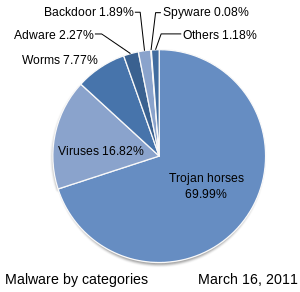
Malware - Wikipedia  What is a Computer Trojan and How it Works?
What is a Computer Trojan and How it Works?  Computer Virus Antivirus Software
Computer Virus Antivirus Software  Trojan Horse Examples \u0026 How to Defend
Trojan Horse Examples \u0026 How to Defend  Methods to Remove Trojan Virus
Methods to Remove Trojan Virus  Trojan Horses
Trojan Horses
UKIP Leadership Candidate Calls For Ban on Muslim Veil in Public how trojan horse attack computer software Police Chief: Post-Brexit Spike in Hate Crime Is Worst on Record how trojan horse attack computer software Bomb Blast at Pakistani Hospital Kills at Least 70, Injures 120 how trojan horse attack computer software Rio Olympics: As Security Concerns Mount, Police Beef Up Patrols how trojan horse attack computer software
how trojan horse attack computer software Gold White Black Red Blue Beige Grey Price Rose Orange Purple Green Yellow Cyan Bordeaux pink Indigo Brown Silver