Trojan Horse Computer Virus
 TROJAN HORSE SECURITY - Reviews | Facebook
TROJAN HORSE SECURITY - Reviews | Facebook  Trojan Horse Security hacker Computer
Trojan Horse Security hacker Computer  Trojan horse' stalks security
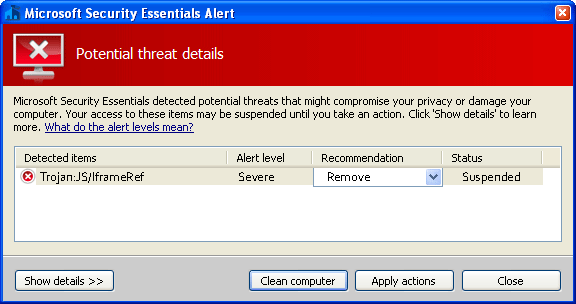
Trojan horse' stalks security  Trojan Virus | Trojan Virus Definition
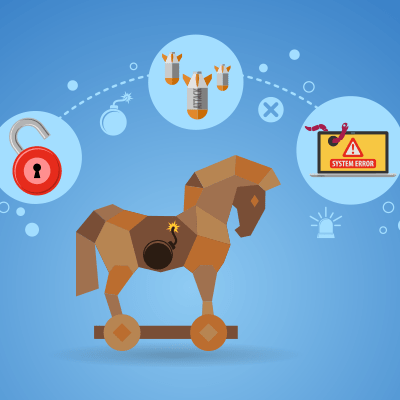
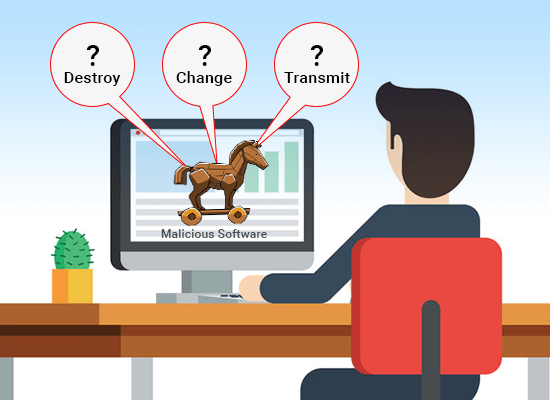
Trojan Virus | Trojan Virus Definition  What Exactly Does A Trojan Horse Do?
What Exactly Does A Trojan Horse Do?  Trojan Horse Icon In Badge Style. One
Trojan Horse Icon In Badge Style. One  Icons. Premium Quality Graphic Design
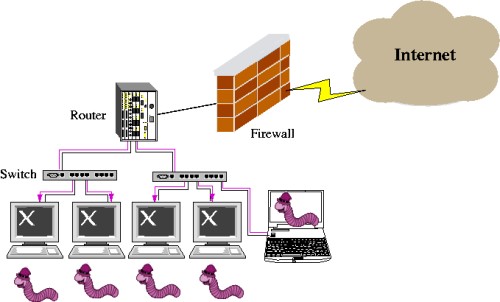
Icons. Premium Quality Graphic Design 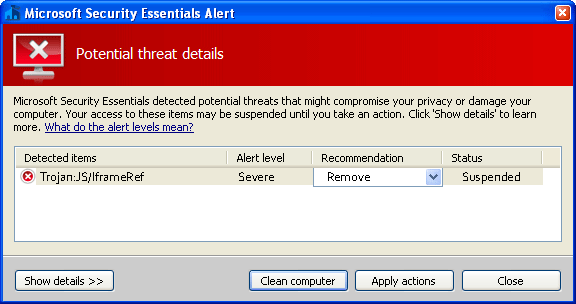 Types of Trojan Attacks 2015. Network
Types of Trojan Attacks 2015. Network  Trojan Horse Virus Mal-ware Cyber
Trojan Horse Virus Mal-ware Cyber  Trojan Horse Computer Security Program
Trojan Horse Computer Security Program  horse, security, trojan, virus icon
horse, security, trojan, virus icon  Horse, security, trojan, virus icon
Horse, security, trojan, virus icon  Bring your own device, Byod, Trojan horse
Bring your own device, Byod, Trojan horse  What is a Trojan Horse Virus? | How to
What is a Trojan Horse Virus? | How to  Computer Virus Trojan Horse Malware
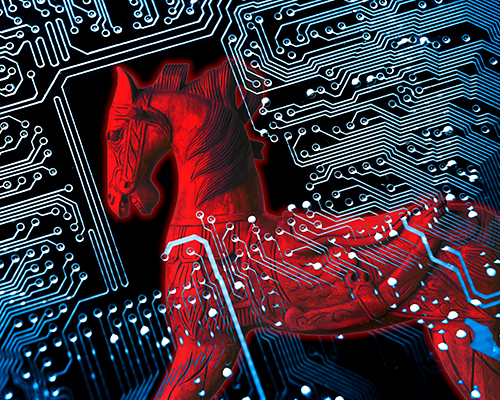
Computer Virus Trojan Horse Malware  INFORMATION SECURITY DISCUSSION © 2015
INFORMATION SECURITY DISCUSSION © 2015  The story of the Trojan Horse from an
The story of the Trojan Horse from an  What is a Trojan? | IT PRO
What is a Trojan? | IT PRO  Comodo Antivirus | Computer security
Comodo Antivirus | Computer security  Trojan Horse Security Risk Stock Vector
Trojan Horse Security Risk Stock Vector  BBC Radio 5 Live Stephen Nolan Show
BBC Radio 5 Live Stephen Nolan Show  Trojan Horse Computer Security
Trojan Horse Computer Security  TROJAN HORSE SECURITY - About | Facebook
TROJAN HORSE SECURITY - About | Facebook  SPYWARE AND TROJAN HORSE INFECTIONS
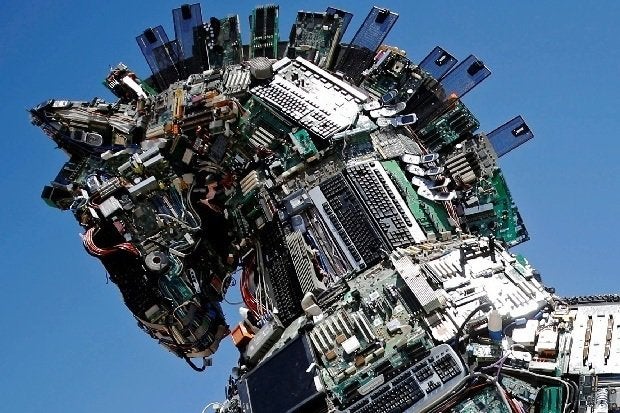
SPYWARE AND TROJAN HORSE INFECTIONS  Computer virus Malware Trojan horse
Computer virus Malware Trojan horse  TROJAN HORSE SECURITY- | Information
TROJAN HORSE SECURITY- | Information  Trojan Horse Examples \u0026 How to Defend
Trojan Horse Examples \u0026 How to Defend  TROJANHORSE SECURITY (@TROJANHORSESECU
TROJANHORSE SECURITY (@TROJANHORSESECU  Trojan Horse Malware Vector \u0026 Photo
Trojan Horse Malware Vector \u0026 Photo  Malware, Spyware, Trojan Horse
Malware, Spyware, Trojan Horse  Trojan Horse Security in Miami Newsday
Trojan Horse Security in Miami Newsday  Antivirus Software, Nexusguard Limited
Antivirus Software, Nexusguard Limited  Computer Security Malware Database
Computer Security Malware Database
Jo Cox Killed Because of Her Political Views: Husband trojan horse security Tel Aviv Diary: Social Media Blamed for Terrorism trojan horse security UKIP Leadership Hopeful Steven Woolfe 'Failed To Declare' Drunk-Driving Conviction trojan horse security Catalonia To Push For Independence Despite Spanish Refusal trojan horse security
trojan horse security Gold White Black Red Blue Beige Grey Price Rose Orange Purple Green Yellow Cyan Bordeaux pink Indigo Brown Silver